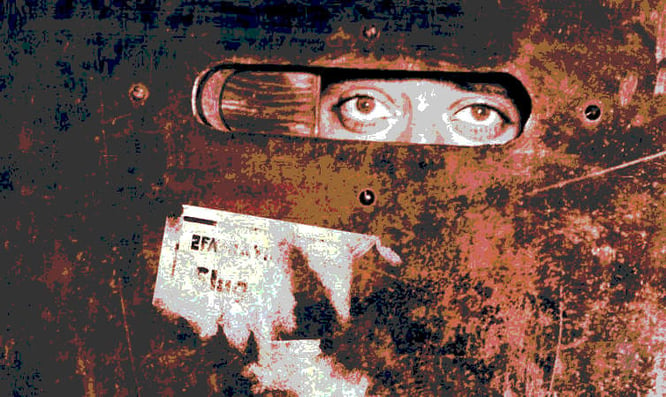
In the days of Prohibition getting your Appletini was much more difficult than it ever should be. Foremost was the fact that they didn't exist. Other than that you would need to know where a speakeasy was, have the password ("Joe sent me"), and not be a copper (the law enforcement kind, not the British penny). In fact this was Multi-factor Authentication: something you know, something you have, and something you are (or are-not in this case). NAPC can help you revisit these roaring 20's but for the 2020s, and perhaps help you cut down on your Appletini consumption in the process.
Multi-factor Authentication or "MFA" is one of the buzz-words of 2016. Everyone is saying it but many people don't quite understand what the mechanism means to their security. It doesn't just mean that it protects against the brute-force attacks we've now had in our system logs for years, it also means more elaborate exploits can be mitigated
Take this years huge growth in spear-phishing attacks. Some of the largest, most security-concious corporations and government entities fell prey to spear-phishing attacks that involved advanced social engineering combined with compromised email accounts. For the attacker access to the victims email account means that they first analyze the communications in the victims inbox and craft an email interaction masquerading as someone the victim knows and convince them to do something that they wouldn't otherwise do, such as wiring money or sending proprietary information.

There are many things you can do to help avoid such a scenario, however MFA is probably the most effective. If all of your internal and privileged resources are protected by MFA then you've short-circuited the attacker at the outset. If the attacker doesn't have the 2nd factor for your email account login then they can't even get started. It doesn't matter if they have password, the 2nd factor prevents them from ever using it.
But attacks aren't just limited to email. Cloud services are effected as well. Whether it's your office suite, your CRM suite, or even your accountiing solution, you really must protect all of your corporate services. Any little bit of information about your company or internal processes can give a smart attacker a leg-up on how to convince your employees into doing something that they probably wouldn't normally do.
Lastly there is what's inside your firewall: people. People have flaws, and mitigating those flaws can make your work an endless nightmare. Many of the things that an employee might do to ruin your weekend aren't necessarily intentional, but nonetheless can make you wish you could crush their skull with a rock. Ok, perhaps that's a bit extreme but the sentiment is similar. Preventing users from being their own worst enemy can extend inside your firewall as well. Adding MFA to servers, desktops, even network hardware will ensure that nobody inadvertantly has access to something that they shouldn't. Also, sharing their account information "for convenience" becomes useless. Also by adding MFA to a tunable privilege escalation mechanism you ensure that they are both the actual person that they say they are and are allowed to do what they are doing, and for everytime they do it.
Contact NAPC today and we can help you navigate all of these issues and address any concerns you might have with reliable, secure solutions from Centrify. NAPC has the expertise in all of these technologies and experience in addressing all of your issues. Whether you have an audit pending or have had an "event" that you need kept confidential, NAPC can help.
